Popular sources of dark web .onion links include Pastebin, Twitter, Reddit, and other Internet forums. Tor is free, open-source software that helps you stay anonymous online. When you browse the internet using Tor browser, your traffic is randomly directed through a network of servers before you reach your final destination, in order to protect your location and identity. Although many developers had been a part of the Invisible IRC Project (IIP) and Freenet communities, there are significant differences between their designs and concepts. Protecting yourself on the Internet is possible in a few different ways, and depending on your needs, you can choose for yourself which solution fits you the best.
This Tor alternative has programmed encryption services that protect its users from trackers and attackers. This is done by encrypting the network traffic thus turning it into a safe and private Tor browser alternative. I2P is like an Internet within the Internet as it builds a network layer within TCP/IP and UDP sessions. This is how I2P becomes an ideal hoard for network traffic and personal data. We can also say that all these abilities make I2P a worthy Tor browser alternative.
Dissenter Review 2020 – The Ad Blocking ‘Free Speech’ Browser by…
Tor Browser has a vast following in the online privacy and security communities. It works by bouncing your communication through numerous encrypted nodes on the internet, making it impossible to determine your location or other identifying information. If you’re careful, you can safely access and browse the dark web. First, download the Tor browser, which will give you access to dark web sites and keep you anonymous while searching the sometimes-seedier corners of the internet. Just like Tor, I2P – Invisible Internet Project – also utilizes DarkNet technology.
These onion routers employ encryption in a multi-layered manner (hence the onion metaphor) to ensure perfect forward secrecy between relays, thereby providing users with anonymity in a network location. That anonymity extends to the hosting of censorship-resistant content by Tor’s anonymous onion service feature. Furthermore, by keeping some of the entry relays (bridge relays) secret, users can evade Internet censorship that relies upon blocking public Tor relays. As of November 2013[update], Tor had about four million users. According to the Wall Street Journal, in 2012 about 14% of Tor’s traffic connected from the United States, with people in “Internet-censoring countries” as its second-largest user base.
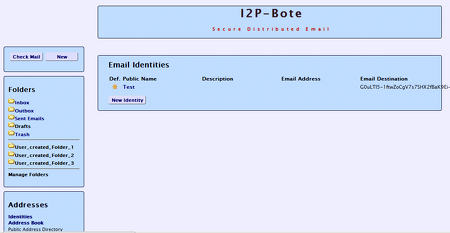
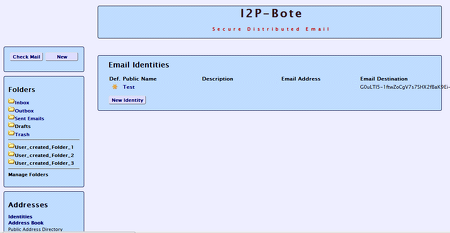
All bote-mails are transparently end-to-end encrypted and signed by the sender’s private key, thus removing the need for PGP or other email encryption software. I2P-Bote offers additional anonymity by allowing for the use of mail relays with variable length delays. Since it is decentralized, there is no centralized email server that could correlate different email identities as communicating with each other (i.e. profiling). The original sender could have gone offline long before the email becomes available to the recipient.
The Tor Project website provides the best practices (instructions) on how to properly use the Tor browser. For example, Tor warns its users that not all traffic is protected; only the traffic routed through the Tor browser is protected. Users are also warned to use https versions of websites, not to torrent with Tor, not to enable browser plugins, not to open documents downloaded through Tor while online, and to use safe bridges. Users are also warned that they cannot provide their name or other revealing information in web forums over Tor and stay anonymous at the same time.
This tor browser alternative provides its user with premium anonymity and online security. This means that even if someone wants to track you down, he will end up finding the Globus servers instead. Tor responded to earlier vulnerabilities listed above by patching them and improving security. In one way or another, human (user) errors can lead to detection.
No account registration is necessary, all you have to do in order to use it is create a new identity. A VPN (Virtual Private Network) encrypts and anonymizes your online data traffic. This means none of your information will be visible, and neither can any of it be traced back to you. A VPN, combined with the options the Tor browser offers, provides you with double protection, making surfing a lot safer.
Several court cases have shown that illegal activities on the dark web can sometimes be traced back to specific individuals using the Tor browser. Hence it seems to be possible to discover and collect a user’s data, including their IP address, even when they are being protected by Tor. In the past, Tor users have been found out because the NSA owned a huge part of the Tor nodes. This was problematic for users who concern themselves with illegal practices.

- I2P (Invisible Internet Project), which is definitely one of the best anonymous peer-to-peer networks available today, allows for censorship-resistant communication.
- The I2P software that implements the encrypted communication layer is called an ‘I2P router’ and any system where it’s running is called the ‘I2P node’.
Is i2p safer than Tor?
The I2P approach is more secure since there are no fixed points (the Directory Servers) to attack. Tor uses two-way encrypted connections between each Relay, while I2P uses one-way connections between every server in its tunnels.

Tor is increasingly used by victims of domestic violence and the social workers and agencies that assist them, even though shelter workers may or may not have had professional training on cybersecurity matters. Properly deployed, however, it precludes digital stalking, which has increased due to the prevalence of digital media in contemporary online life.
Turbo VPN Review for 2020 Free Mobile VPN, Not Worth the…
Tor can also provide anonymity to websites and other servers. Servers configured to receive inbound connections only through Tor are called onion services (formerly, hidden services).
What Is I2P & How Does It Compare vs. Tor Browser?
The moment those users are identifiable, the police can track them down and arrest them. iPrediaOS is a Linux based OS, and it is one of the plausible Tor browser alternatives available.
Also, on December 2016, Turkey has blocked the usage of Tor, together with ten of the most used VPN services in Turkey, which were popular ways of accessing banned social media sites and services. In 2011, the Dutch authority investigating child pornography found out the IP address of a Tor onion service site called “Pedoboard” from an unprotected administrator’s account and gave it to the FBI who traced it to Aaron McGrath. Onion services can also be accessed from a standard web browser without client-side connection to the Tor network, using services like Tor2web.
What does I2P do for you?
It’s an anonymous network primarily created to keep its users hidden and protected from government surveillance and third-party monitoring on the web. Currently, it serves mostly as a way of securely accessing the Darknet. It’s encrypted, which makes it great for users who want to hide their identity.
Rather than revealing a server’s IP address (and thus its network location), an onion service is accessed through its onion address, usually via the Tor Browser. The Tor network understands these addresses by looking up their corresponding public keys and introduction points from a distributed hash table within the network. It can route data to and from onion services, even those hosted behind firewalls or network address translators (NAT), while preserving the anonymity of both parties. Tor aims to conceal its users’ identities and their online activity from surveillance and traffic analysis by separating identification and routing. It is an implementation of onion routing, which encrypts and then randomly bounces communications through a network of relays run by volunteers around the globe.
Along with SecureDrop, Tor is used by news organizations such as The Guardian, The New Yorker, ProPublica and The Intercept to protect the privacy of whistleblowers. I2P-Bote(github) is a free, fully decentralized and distributed anonymous email system with a strong focus on security. It supports multiple identities and does not expose email metadata. I2P-Bote is accessible via the I2P web console interface or using standard email protocols (i.e. IMAP/SMTP).
I2P (Invisible Internet Project), which is definitely one of the best anonymous peer-to-peer networks available today, allows for censorship-resistant communication. The anonymity of the communication is achieved with end-to-end encryption of user’s traffic and then sending the same through a volunteer-run network of about 55 thousand computers that are distributed around the world. The I2P software that implements the encrypted communication layer is called an ‘I2P router’ and any system where it’s running is called the ‘I2P node’. A free, open source OS, I2P is faster than the Tor browser and selects peers on the basis of continuous ranking and profiling. Globus is a paid Tor browser alternative that offers a 5-day free trial version as well.